What on Earth is Agile Risk Analytics?
August 30, 2017
[Note: ‘Risk’ is one of those words that has lots of interpretations. So for clarity, we’re defining ‘risk’ here as either: a) exposure to compromise of something the business cares about deeply by a credible threat actor; or b) confirmed compromise that exposes the business to unacceptable impact.]
TL;DR — ARA (as we’ll call it for short) is the capability to get increasingly meaningful and timely insights about risk, from a varied and ever-expanding number of security-relevant data sources.
In ‘operational/process terms’, this means being able to:
- ingest, model, explore, enrich and correlate data sets at enterprise scale, with ease and speed
- root your analysis in the context of operational ‘entities’ (e.g. users, computers, apps) that support critical business services and revenue generation
- put results in the context of business and IT processes, (comparing ‘now’ vs ‘beginning of time’ if you want to identify those pesky systemic issues that only surface when you analyse long-term trends)
- ‘radar sweep’ for risk (at Panaseer we call this ‘risk hunting’) by by number crunching whatever data you want at any frequency using any analysis technique
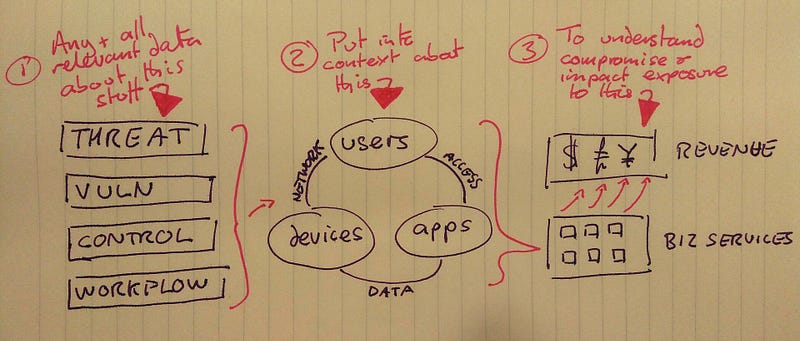
They say a picture paints 1000 words (…although this picture is mainly words so I’m not sure it even qualifies as a picture…)
In ‘practical example terms’ here’s what this means:
“I want to take our #n-thousand customers, our #n-thousand devices, our who knows how many #n-users/developers, blah blah blah. I want to take data about all those entities that revenue and critical business services depend on, and I want to run referential integrity checks across all of it; the databases, the streaming sources, the digital exhaust from business and IT workflow; the data from security controls; all the logs we have.
And at whatever frequency I choose, I want to crunch that data to know:
– What’s in my environment? What’s new, what’s it connecting to, is it legit?
– Is my environment being managed as expected?
– Is process being followed or subverted?
– Is there a control gap, technical or process-wise, that needs closing?
– Is everything OK with workflow and controls, but there’s something I can only detect in the logs, which I need my SOC’s sniper scope to be zoned in on?
– What can I push aside in the logs as stuff I don’t care about, vs stuff that needs to be pushed up the chain right to Board level right now?
And then I want to take all of that, and bubble it up to a view that tells my CISO and the people he sits in meetings with all day “Here is where we shift our resources this week or this month or right now today, in order to get the biggest uplift to the protection of what matters most to our business.”And with all that, I want the confidence in the integrity and accuracy and consistency of the data to be able to automate workflow off the back of that.Then at any point, I want to pull in another data source and re-run all of my questions to either get better resolution of the ground at 50,000 ft, or zoom in right to the number plates on the cars driving down a specific street at ground level.Oh, and I’d like all that in hours or minutes please, rather than it taking months or weeks, or not being possible at all.– Security Analytics Lead somewhere in an Investment Bank in NY