- How we help
- Platform
- Solutions
- About
- Resources
Solutions
Are your security controls working effectively?
Measure and optimize your security posture using Continuous Controls Monitoring, with actionable insights that improve prioritization and accelerate remediation.
Trusted visibility of security controls
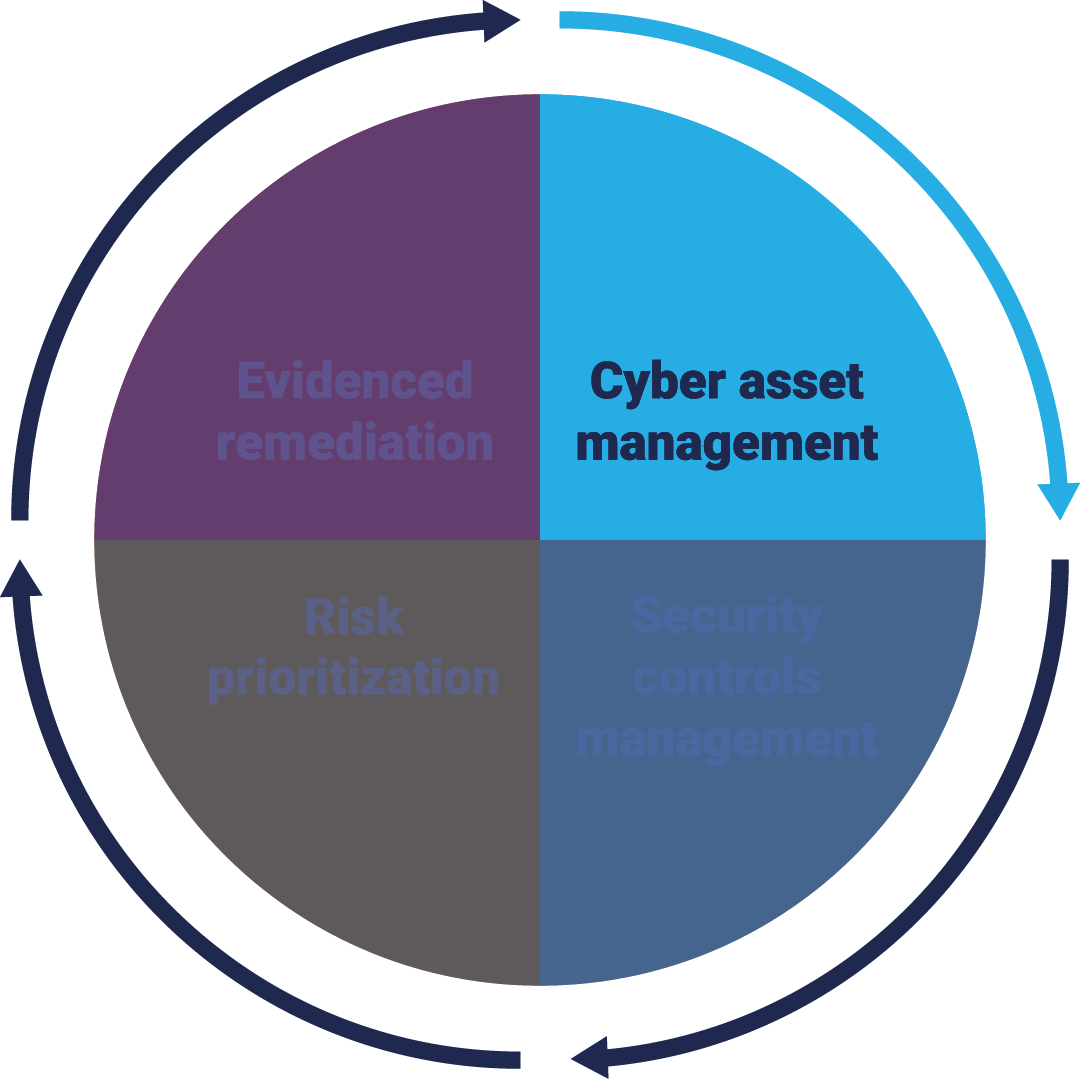
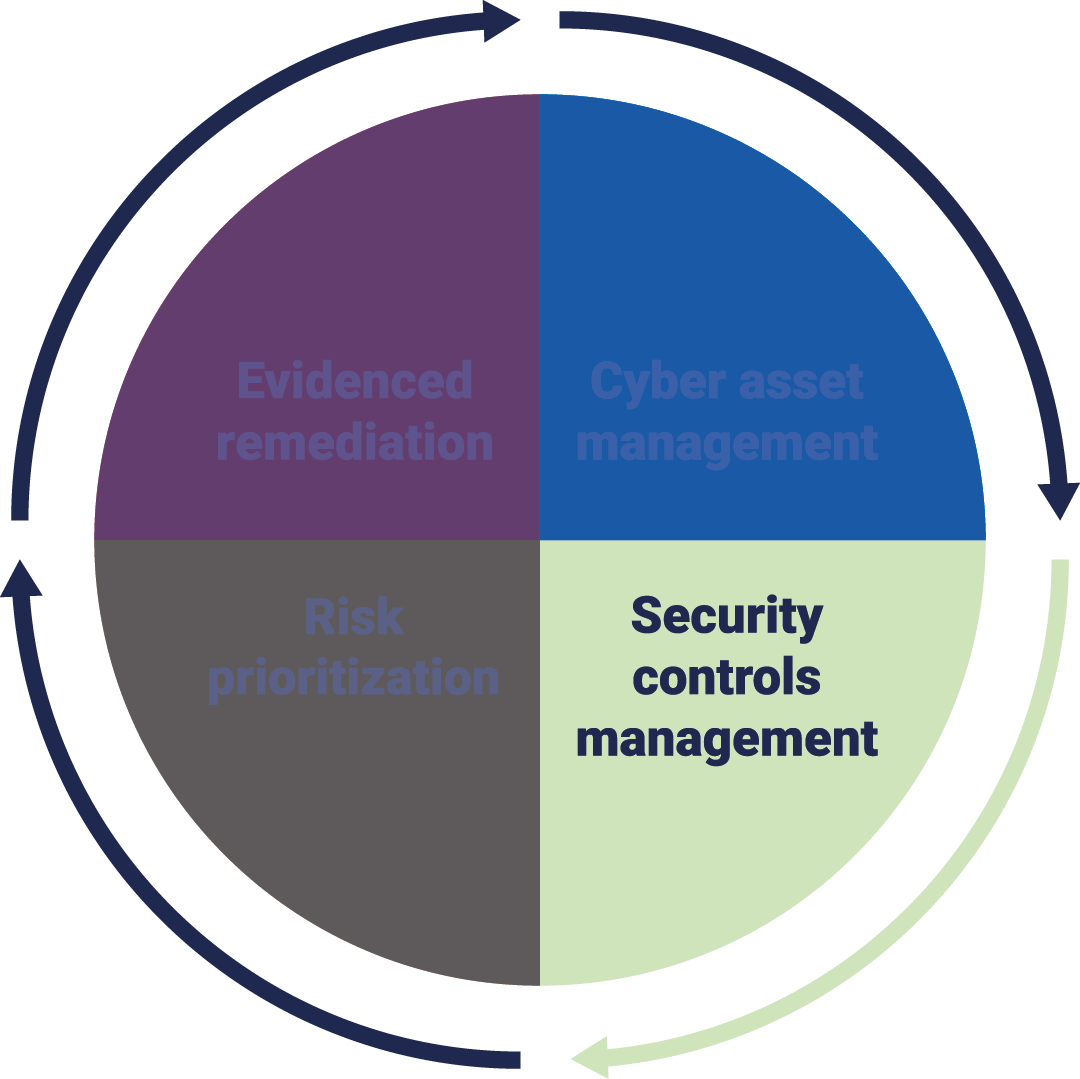
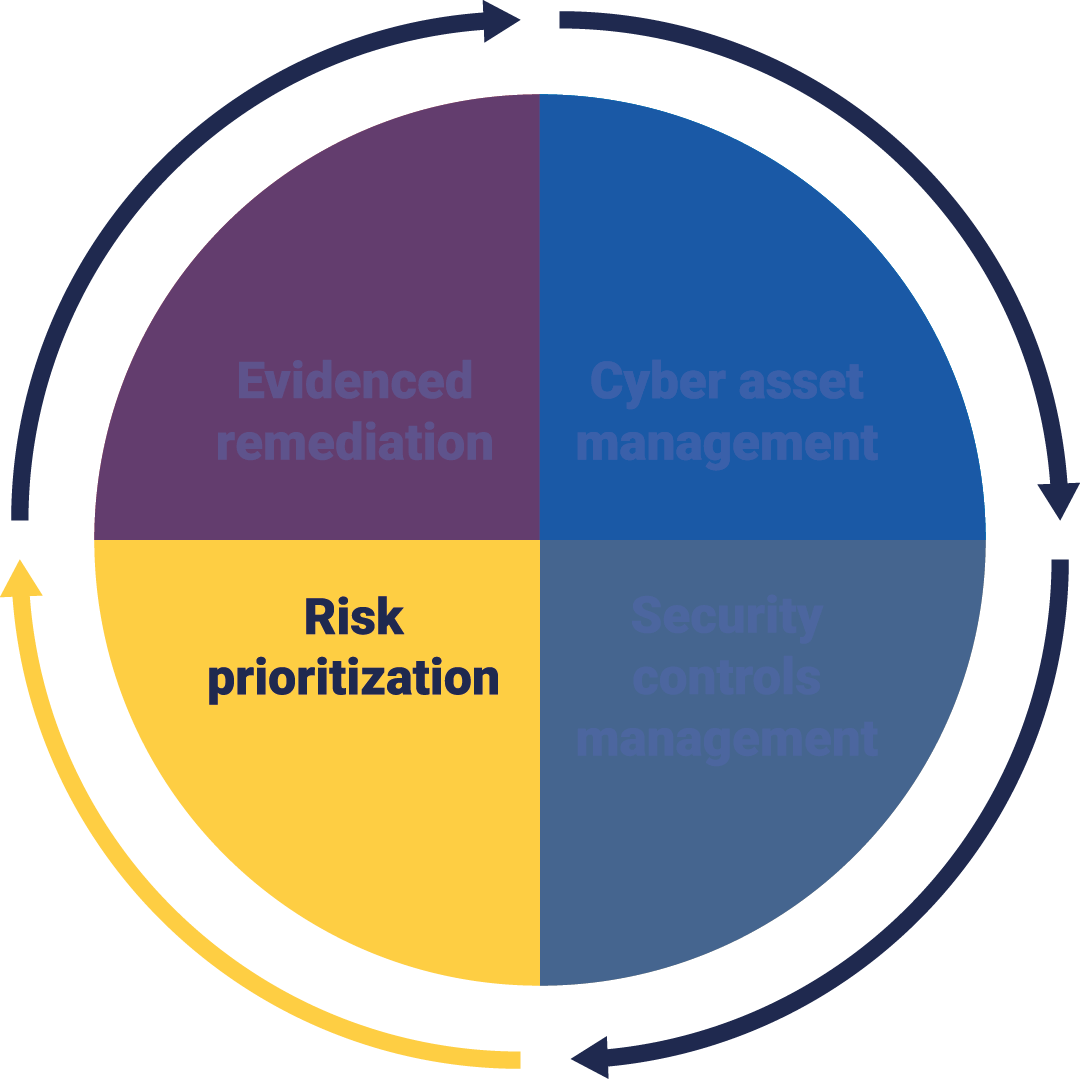
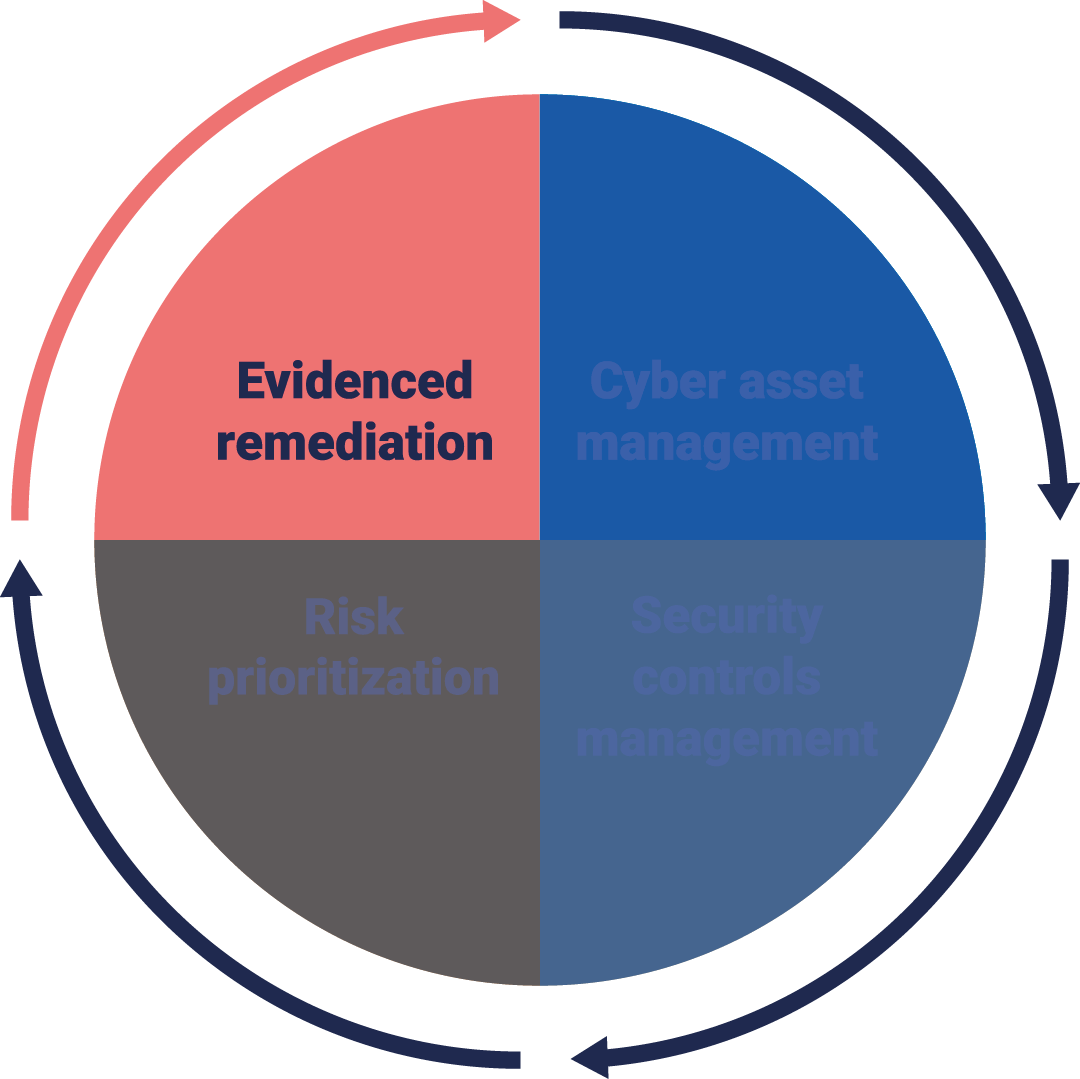
Stages of Continuous Controls Monitoring
Not all security risks are created equal. Save time, improve decision making and rapidly reduce your cyber risk with automated prioritization.
By understanding the context behind controls data, including ownership and business processes, you can target remediation efforts towards the most critical risks.
Move away from reliance on subjective validation and reduce the risk of human error with a trusted, data-driven view of the status of remediation campaigns.
Data from your existing security tools is used to evidence when issues have been fixed, so you can track remediation against your own policies and SLAs, and improve accountability.
Benefits of the Panaseer Platform
Total visibility
Get a trusted, automated inventory of all assets, accounts, apps and cloud systems by combining data from across your security and business tools.
Total visibility
Get a trusted, automated inventory of all assets, accounts, apps and cloud systems by combining data from across your security and business tools.
Confident decision-making
Actionable insights show you what to prioritize based on business risk, ensuring you can deploy resources where they’re needed most.
Confident decision-making
Actionable insights show you what to prioritize based on business risk, ensuring you can deploy resources where they’re needed most.
Improved accountability and efficiency
Evidenced remediation improves accountability by tracking fixes against your policies and SLAs, while automated reporting saves time and frees your people to focus on critical tasks.
Improved accountability and efficiency
Evidenced remediation improves accountability by tracking fixes against your policies and SLAs, while automated reporting saves time and frees your people to focus on critical tasks.