Why cyber hygiene is our most important defence against ransomware
December 08, 2022
We really need to talk about ransomware…
The one topic that always comes up when discussing cybersecurity is ransomware. Whether it’s due to the latest outage impacting critical infrastructure, a small business worried about the existential threat it presents, or large corporations trying to understand their overall exposure to ransomware, it’s clear we’ve not solved the challenge yet. The stats on ransomware make depressing reading…
Are things getting better or worse? Is there a silver bullet? Sometimes vendors seem to suggest it is with research and reports. But is it?
Recent ransomware research
There’s been some great insight published recently. Notably from Microsoft’s 2022 Digital Defense Report and a collaboration from Arete and Cyentia entitled Reining in Ransomware. Arete focuses purely on ransomware, whereas Microsoft looks widely at global issues with a deep dive into cybercrime.
There have also been detailed forensic analyses of major ransomware incidents that have been made public, such as the Irish Healthcare supplier attack. And there’s great research from companies like CrowdStrike, which saw an 82% increase in data leaks from ransomware in 2021 from the previous year.
What can we, the cybersecurity community, take from all of this?
Primarily: getting cyber hygiene right is key.
Secondly: cyber hygiene is hard.
Thirdly: it’s the things you thought you’d covered that leave you exposed. See: hygiene.
Let’s look at these in a bit more depth…
What is cyber hygiene?
Saying “cyber hygiene is the answer” is, I’m fairly sure, going to grate with some people. It’s almost as triggering as saying “cybersecurity is easy”, which it isn’t, or “pineapple belongs on pizza”.
In November 2022, Microsoft said basic cyber hygiene will still protect you against 98% of attacks. The Arete report notes that phishing and valid account usage are two of the top “first steps” in ransomware attacks, which both would fall under the realm of hygiene.
But what is cyber hygiene? Basic hygiene means having “basic” security controls in place. Specifically, multi-factor authentication, patching, using allowed and blocked app lists, making backups, and using anti-malware. Patching would also help with the most common first point of infection according to Arete, which is External Remote Services. Generally speaking, these are controls that most enterprises will already have in place.
It sounds like I’m saying this is an easy thing to fix.
But in an enterprise, you have to do that for thousands of people, accounts, and devices.
Cyber hygiene in the enterprise
In an enterprise environment, things aren’t that straightforward. There are so many devices to protect, and changing things brings unintended consequences. MFA is a mere fig leaf if legacy authentication is still enabled. And turning that off means you have to update all your apps that are relying on it. The old ones that don’t use modern authentication. The ones that you may not have the source code for any more…
As evidenced by the Uber hack though, this is a price we must be willing to pay, otherwise the scripts that have your vault’s admin username and password will be used against you. “Just turn on MFA” is a breaking change for almost every organisation as the reality is really “turn on MFA and turn off legacy authentication”, but it’s absolutely non-negotiable.
It’s made harder still as Microsoft has changed its view of “basic cyber hygiene” between 2021 and 2022, and one of the five things it recommends to get 98% protection is “apply zero trust principles”. In Microsoft parlance, that’s “verify explicitly”, “use least privilege”, and “assume breach”. Sounds easy. So why are all Microsoft employees local admins on their machines? That doesn’t really meet their second tenet. Basic cyber hygiene is evolving, as it should, and getting harder to reach.
We’re all familiar with the concept of technical debt caused through a deliberate decision not to invest, and it looks like hygiene debt is another thing we need to measure.
Why is this so hard?
A timely tweet from Lisa Forte of Red Goat Cyber summarises well.
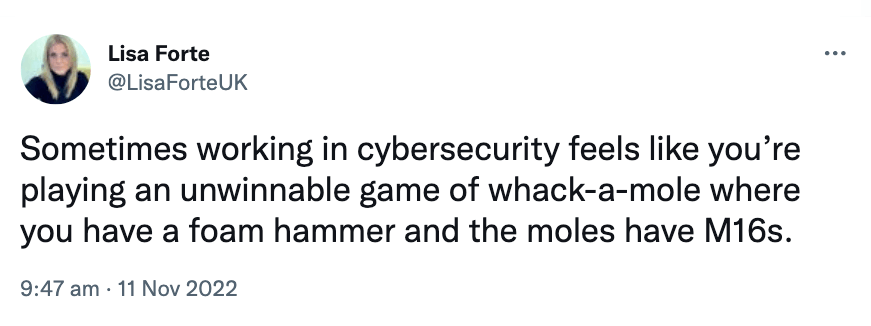
As noted above, ransomware-as-a-service is equipping our moles with M16s with no real risk, and no real barrier to entry. The moles can probe every part of the attack surface, launch password sprays or brute force attacks, phish and social engineer at scale.
The attacker only needs to get lucky once. Defenders need to get lucky every time.
So, we can’t rely on luck.
And that means knowing, with certainty, that your assets are protected, and the attack surface they present is managed.
Vendors are doing really smart stuff. For example, at Microsoft’s Ignite showcase this year, they announced automated attack disruption, which will take assets off a network if an in-flight attack is found on a machine. This is clever stuff — however it only acts on what it knows about. If your endpoint doesn’t have MDE turned on, or isn’t managed by SCCM, it won’t help.
Your defence, and a meaningful way to provide the foundation of your security posture, starts with an asset inventory. That sounds straightforward, but, I couldn’t say with certainty how many computers I have in my house, and what state they’re in. So, it will be exponentially harder at any organisation.
As such, your asset inventory needs to take every source it can and use that as its starting point. And then you’ve got to deduplicate things. That’s non-trivial, but achievable with automation and data science witchcraft. If something is picked up by a discovery tool that isn’t in your CMDB, it still needs evaluating, assessing, patching, protecting and more. Otherwise, it’s somewhere an adversary can get lucky and start their ransomware attack.
Measuring security for fun and profit
How can you be sure you’re best protected against ransomware? Measure your posture. This sounds like a trite saying up there with “put basic cyber hygiene in place”, however it is giving you an approach that you can use to discover what your hygiene state actually is, and what you can do to improve it.
You measure controls. Starting with inventory controls: do you know all your assets? Your assets aren’t just hardware or VMs (virtual machines), they’re anything that can be used to produce value for your organisation. That’s hardware, but also software, locations, capital, intellectual property, employees, knowledge.
At this point, policy comes into play: you will have chosen to protect your assets with appropriate security controls. You need to measure that those controls are actually in place against your assets. You need to measure coverage. This in turn can give you a view of your policy compliance.
Add in business context, and you’ve got a way to prioritise your assets. And then you can move to ensuring you’ve got the right insight to know what to do next.
It sounds like I’m saying all this is easy: it isn’t. There are huge challenges around ransomware and security in general. For me, three months after leaving Microsoft, I am convinced that the biggest challenge facing the security industry is one of security control failures or gaps.
And I’m convinced that finding those gaps, and measuring your posture as a result, then diagnosing and prioritising remediation based on business criticality, is the most meaningful approach to stopping the game of whack-a-mole, and ultimately making the digital world a little safer.